Introduction: The Fragility of Trust
In software engineering, and especially in AI, the act of deploying code is no longer a purely technical gesture—it is an act of trust. We trust the pipeline to safeguard sensitive data, the infrastructure to comply with regulations, and the organization to honor the confidence placed in it by clients, governments, and society at large. A single failure in security or compliance is no longer a private mishap; it reverberates through legal systems, public perception, and even the moral standing of the company.
This article explores how secure, compliant deployment pipelines for AI are built and maintained—not just as a technical challenge, but as a philosophical practice of responsibility, reflection, and discipline.
The Pipeline as a Mirror of Character
Philosophers like the Stoics remind us that external events are beyond our control, but our internal practices are not. Marcus Aurelius wrote, “The soul becomes dyed with the color of its thoughts.” In the same way, a deployment pipeline becomes dyed with the principles of its builders.
If we treat compliance as an afterthought, the pipeline will reflect neglect. If we treat security as a bolt-on, the pipeline will leak. But if we integrate rigor, transparency, and accountability from the first line of code to the last deployment step, the pipeline becomes a reflection of disciplined engineering character.
Why Security and Compliance Matter More in AI
The Unique Risk of AI Systems
AI applications are not static; they learn, adapt, and infer. This dynamism introduces risks far greater than traditional software:
- Data sensitivity: Training data often includes personally identifiable information (PII) or regulated data sets.
- Unpredictable behavior: A model may drift, hallucinate, or generate biased outputs.
- Opaque reasoning: Explaining decisions for audit or compliance purposes can be difficult.
The Legal and Ethical Landscape
Compliance is not merely about avoiding fines. Laws like GDPR, HIPAA, and CCPA demand accountability, transparency, and user rights. For AI systems, this means:
- Demonstrating how models are trained and monitored.
- Ensuring data lineage is traceable.
- Providing explanations for automated decisions.
Failure is costly—not only in financial penalties, but in broken trust with customers and regulators.
Foundations of a Secure Deployment Pipeline
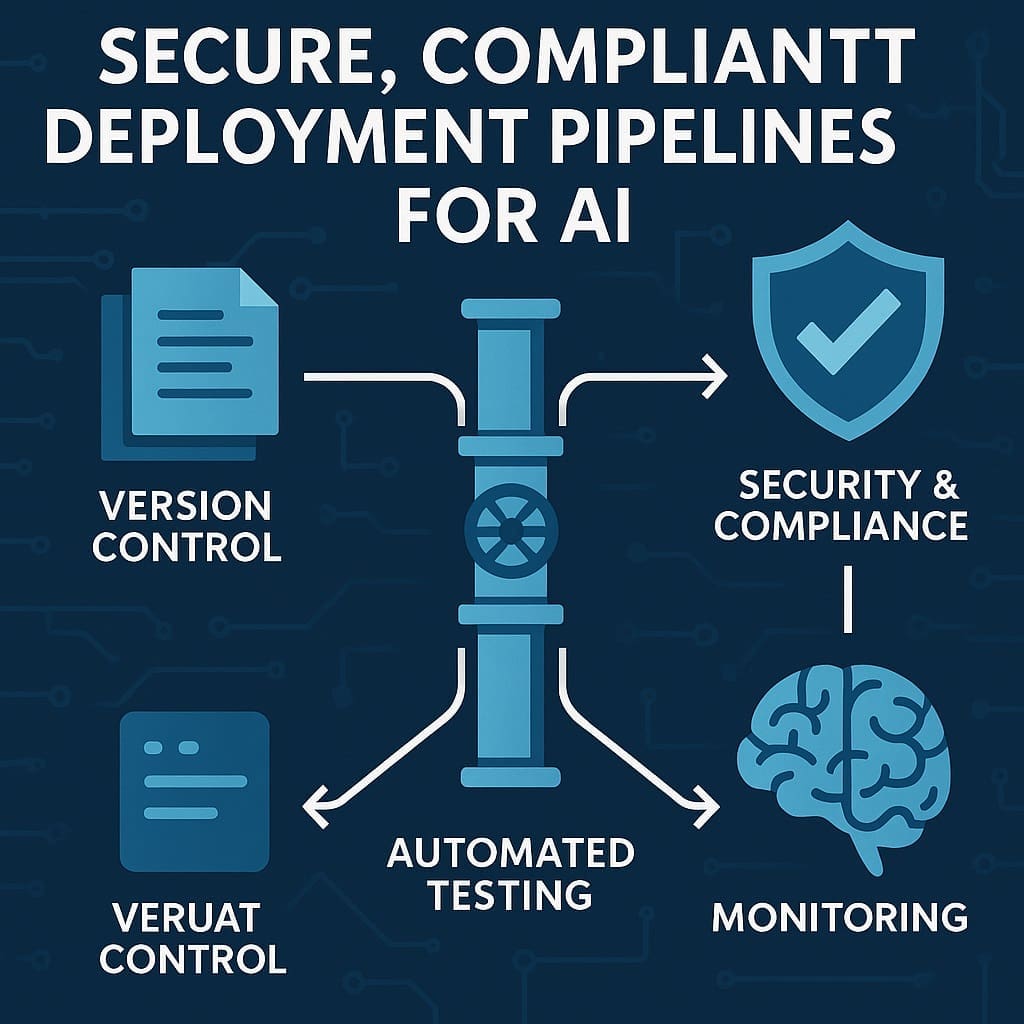
A professional-grade deployment pipeline must include:
- Version Control Discipline
Every change—code, model, or configuration—should be tracked. This ensures reproducibility, auditability, and rollback safety. - Automated Testing and Validation
- Unit tests for code correctness.
- Data validation tests for input quality.
- Bias and fairness checks for models.
- Identity and Access Management (IAM)
Restrict who can deploy, access data, or modify models. Role-based access is essential for both security and compliance. - Encryption and Data Protection
Encrypt data in transit and at rest. Protect model artifacts the same way you protect sensitive data. - Continuous Monitoring
- Detect model drift.
- Log access to sensitive systems.
- Alert on anomalies in real-time.
- Immutable Deployments
Deployments should be reproducible and verifiable. If you cannot reproduce an environment exactly, you cannot prove compliance.
Compliance by Design: Building for Auditors, Not After Them
Many organizations treat compliance as paperwork added after development. This mindset is outdated. Instead, compliance must be woven into the pipeline:
- Audit Trails: Every training run, deployment, and rollback must leave a verifiable record.
- Policy as Code: Compliance requirements (like data retention or access controls) should be encoded into scripts, not human memory.
- Explainability Hooks: Even if explainability is imperfect, include mechanisms to log decisions, track inputs, and surface rationales.
Think of this as “designing for the inspector.” Just as a master carpenter builds joints that will hold long after inspection, engineers should build pipelines that naturally demonstrate compliance without scrambling for evidence later.
The Philosophical Reflection: Discipline Over Expediency
Stoicism offers a useful lens: the tension between expediency and virtue. In AI development, expediency says, “Ship it fast; we’ll secure it later.” Virtue responds, “Nothing worthwhile is secure if built on negligence.”
The philosopher Epictetus reminded his students that discipline is not about constraint but about freedom—the freedom that comes when you no longer fear collapse. Likewise, secure and compliant pipelines free organizations from the anxiety of hidden flaws or looming audits.
An unsecure pipeline is like a hollow statue—impressive in form, fragile in substance. A compliant, secure pipeline is like a stone column—difficult to build, but enduring.
The .NET and Microsoft Ecosystem Advantage
For professionals working in the Microsoft and .NET ecosystem, the good news is that the tools for secure and compliant pipelines are already robust:
- Azure DevOps Pipelines provide end-to-end automation with built-in compliance controls.
- Azure Policy and Blueprints allow organizations to encode compliance requirements into infrastructure as code.
- ML.NET and ONNX integrate naturally into .NET applications, ensuring model deployment stays inside familiar, governable environments.
- Defender for Cloud offers real-time threat detection and compliance auditing for AI services running in Azure.
Executives and professionals should see these not as optional features, but as philosophical commitments: to build AI pipelines that reflect rigor, transparency, and accountability.
Case Example: A Bank’s AI Deployment
Consider a financial institution deploying an AI model to detect fraud. Without secure, compliant pipelines:
- A developer could unintentionally push untested code into production.
- A model trained on unvetted data could introduce bias.
- An auditor could request lineage records that simply do not exist.
With secure, compliant pipelines:
- Every change is reviewed, logged, and tied to a ticket.
- Automated bias checks flag anomalies before deployment.
- Encryption, monitoring, and IAM ensure both legal compliance and customer trust.
The difference is not just technical—it is existential for the business.
Conclusion: The Moral Weight of Pipelines
A secure, compliant deployment pipeline for AI is more than an engineering artifact—it is a moral statement. It declares: We value trust over speed. We value transparency over shortcuts. We value responsibility over negligence.
For executives and professionals in the Microsoft/.NET ecosystem, the challenge is clear: leverage the tools already at hand to embed virtue into your AI pipelines. Treat compliance as philosophy embodied in code. Treat security as a reflection of character.
In doing so, you will not only build better pipelines—you will build better organizations.
Want More?
- Check out all of our free blog articles
- Check out all of our free infographics
- We currently have two books published
- Check out our hub for social media links to stay updated on what we publish